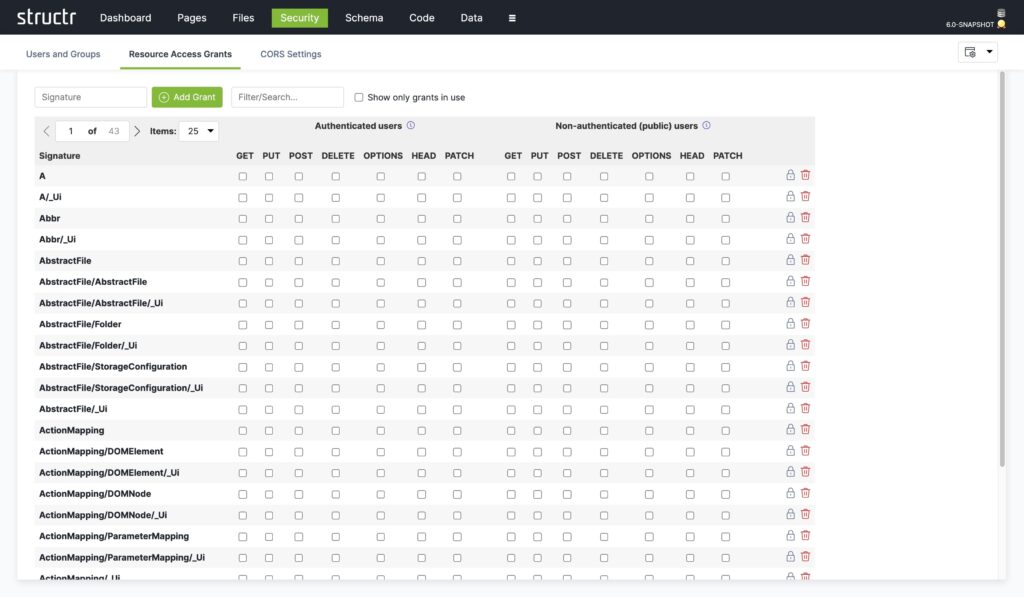
Ensure maximum security with Structr’s customizable access control system. Define users, groups, roles, and permissions at type, schema, and object levels for tailored protection. Our system supports hierarchical group structures, LDAP synchronization, and various authentication protocols. Benefit from fast rights resolution with graph database technology, ensuring efficient and secure access management for complex enterprise needs.